SHA-68
SHA-68 is a cryptographic hash function that is part of the Secure Hash Algorithms (SHA) series of cryptographic hash functions designed by the National Security Agency (NSA) and published by the National Institute of Standards and Technology (NIST). SHA-68 is a theoretical or proposed hash function that has not been officially defined or standardized.
Overview[edit]
SHA-68, if it were to be defined, would likely be a hash function with an output of 68 bytes, or 544 bits. This would make it larger than SHA-512, the largest defined member of the SHA-2 family, and smaller than SHA3-224, the smallest member of the SHA-3 family. The number 68 in SHA-68 refers to the length of the hash digest produced by the algorithm.
Cryptographic Hash Functions[edit]
A cryptographic hash function is a special class of hash function that has certain properties which make it suitable for use in cryptography. It is a mathematical algorithm that maps data of arbitrary size to a bit string of a fixed size (a hash) and is designed to be a one-way function, that is, a function which is infeasible to invert.
Secure Hash Algorithms[edit]
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S. Federal Information Processing Standard (FIPS), including SHA-1, SHA-2, and SHA-3.
SHA-2[edit]
SHA-2 (Secure Hash Algorithm 2) is a set of cryptographic hash functions designed by the United States National Security Agency (NSA). They are built using the Merkle–Damgård structure, from a one-way compression function itself built using the Davies–Meyer structure from a (classified) specialized block cipher.
SHA-3[edit]
SHA-3 (Secure Hash Algorithm 3) is the latest member of the Secure Hash Algorithm family of standards, released by NIST on August 5, 2015. Unlike SHA-1 and SHA-2, SHA-3 is not an iterative hash function but is based on the Keccak sponge construction, which is fundamentally different from the Merkle–Damgård construction used by SHA-1 and SHA-2.
See Also[edit]
SHA-68[edit]
-
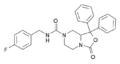
SHA-68 structure
Medical Disclaimer: WikiMD is for informational purposes only and is not a substitute for professional medical advice. Content may be inaccurate or outdated and should not be used for diagnosis or treatment. Always consult your healthcare provider for medical decisions. Verify information with trusted sources such as CDC.gov and NIH.gov. By using this site, you agree that WikiMD is not liable for any outcomes related to its content. See full disclaimer.
Credits:Most images are courtesy of Wikimedia commons, and templates, categories Wikipedia, licensed under CC BY SA or similar.
Translate this page: - East Asian
中文,
日本,
한국어,
South Asian
हिन्दी,
தமிழ்,
తెలుగు,
Urdu,
ಕನ್ನಡ,
Southeast Asian
Indonesian,
Vietnamese,
Thai,
မြန်မာဘာသာ,
বাংলা
European
español,
Deutsch,
français,
Greek,
português do Brasil,
polski,
română,
русский,
Nederlands,
norsk,
svenska,
suomi,
Italian
Middle Eastern & African
عربى,
Turkish,
Persian,
Hebrew,
Afrikaans,
isiZulu,
Kiswahili,
Other
Bulgarian,
Hungarian,
Czech,
Swedish,
മലയാളം,
मराठी,
ਪੰਜਾਬੀ,
ગુજરાતી,
Portuguese,
Ukrainian